13 May 2026 | News
Penetration testing is a security assessment where vulnerabilities are found and exploited, safely, to see the impact a real attack could have.
Ethical hacking is not simply an aggregate of different types of assessments: it is the actions organisations take to pro-actively identify vulnerabilities in their security posture which would give rise to business risk.
When you need facts about the actual state of your security, our security assessments can help. Whether it’s understanding and emulating what a real threat actor could do in your environment, or a scientific and thorough enumeration of all potential vulnerabilities in an application or network – our SensePostTeam can help.
Our research-lead approach means that our teams are on the cutting edge of their field and can be evaluated by their public research contributions through papers, tooling, and conference presentations.
A critical part of our business is our hacking training facility, which we deliver via SensePost, the specialist pen-testing arm of Orange Cyberdefense.
Facts about the actual state of your security
Comprehensive and flexible approaches specific to your goals
A senior and experienced team available
Regular public research contributors
A critical part of our business is our hacking training facility, which we deliver via SensePost, the specialist pen testing arm of Orange Cyberdefense.
Our hacking training courses have taught thousands of students about the art of offensive and defensive approaches. Understand how hackers think, the tools, tactics and techniques they use. Our course presents technical skills and basic concepts required to those desiring a foundation in the world of information security.
Our courses are developed from the work we perform for clients so that you get a better understanding of how to exploit real-world scenarios. As one of Black Hat briefings longstanding training partners, our courses have taught thousands of students about the art of offensive and defensive approaches.
13 May 2026 | News
19 May 2026 | News

12 May 2026 | News
13 April 2026 | News

6 May 2026 | Blog

[Webinar] Mythos: Unpacking the phenomenon and its impact on your cybersecurity
[Webinar] Mythos: Unpacking the phenomenon and its impact on your cybersecurity
Event detailsOnline
28th of May

30 April 2026 | Report
20 April 2026 | Blog
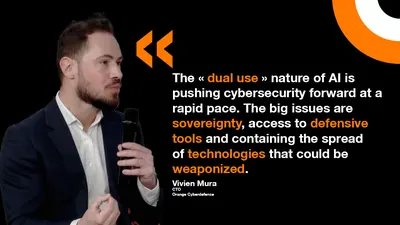
The “dual use” nature of AI is pushing cybersecurity forward at a rapid pace. The big issues are sovereignty, access to defensive tools and containing the spread of technologies that could be weaponized.

DEF CON 34
DEF CON 34
There are hacker conferences… and then there’s DEF CON. As part of DEF CON Training, the SensePost team will be in Las Vegas delivering hands-on, practitioner-led training designed to reflect real-world attack scenarios. Join us!
Event detailsIn-Person
10th of Aug

13 April 2026 | News