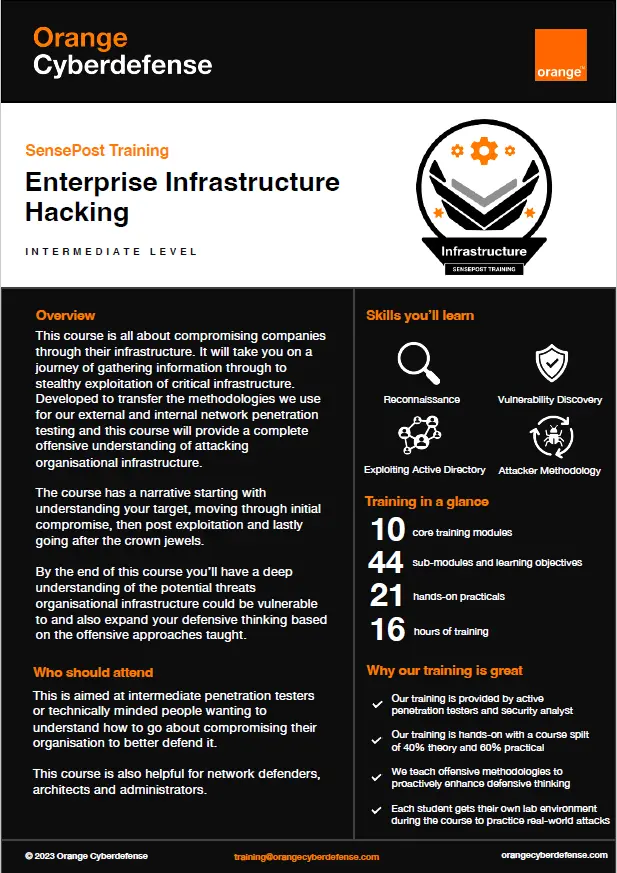
SensePost training: Entreprise Infrastructure Hacking
This course is all about compromising companies through their infrastructure. It willtake you on a journey of gathering information through to stealthy exploitation of critical infrastructure. Developed to transfer the methodologies we use for our external and internal network penetration testing and this course will provide a complete offensive understanding of attacking organisational infrastructure.
The course has a narrative starting with understanding your target, moving through initial compromise, then post exploitation and lastly going after the crown jewels.
By the end of this course you’ll have a deep understanding of the potential threats organisational infrastructure could be vulnerable to and also expand your defensive thinking based on the offensive approaches taught.
Download our brochure