
12 November 2013

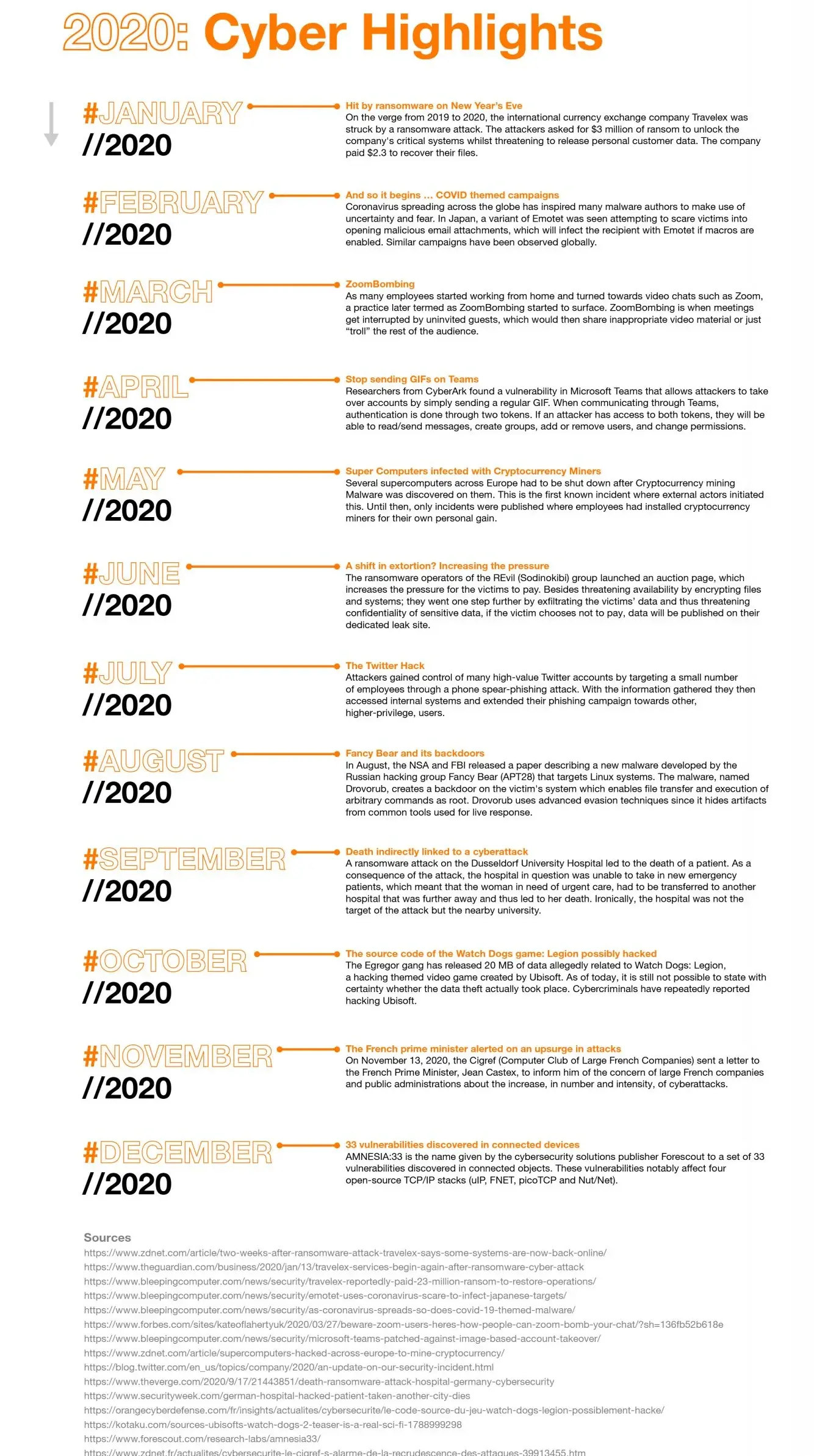
On the verge from 2019 to 2020, the international currency exchange company Travelex was struck by a ransomware attack. The attackers asked for $3 million of ransom to unlock the company’s critical systems whilst threatening to release personal customer data. The company paid $2.3 to recover their files.
Coronavirus spreading across the globe has inspired many malware authors to make use of uncertainty and fear. In Japan, a variant of Emotet was seen attempting to scare victims into opening malicious email attachments, which will infect the recipient with Emotet if macros are enabled. Similar campaigns have been observed globally.
As many employees started working from home and turned towards video chats such as Zoom, a practice later termed as ZoomBombing started to surface. ZoomBombing is when meetings get interrupted by uninvited guests, which would then share inappropriate video material or just “troll” the rest of the audience.
Researchers from CyberArk found a vulnerability in Microsoft Teams that allows attackers to take over accounts by simply sending a regular GIF. When communicating through Teams, authentication is done through two tokens. If an attacker has access to both tokens, they will be able to read/send messages, create groups, add or remove users, and change permissions.
Several supercomputers across Europe had to be shut down after Cryptocurrency mining Malware was discovered on them. This is the first known incident where external actors initiated this. Until then, only incidents were published where employees had installed cryptocurrency miners for their own personal gain.
The ransomware operators of the REvil (Sodinokibi) group launched an auction page, which increases the pressure for the victims to pay. Besides threatening availability by encrypting files and systems; they went one step further by exfiltrating the victims’ data and thus threatening confidentiality of sensitive data, if the victim chooses not to pay, data will be published on their dedicated leak site.
Attackers gained control of many high-value Twitter accounts by targeting a small number of employees through a phone spear–phishing attack. With the information gathered they then accessed internal systems and extended their phishing campaign towards other, higher-privilege, users.
In August, the NSA and FBI released a paper describing a new malware developed by the Russian hacking group Fancy Bear (APT28) that targets Linux systems. The malware, named Drovorub, creates a backdoor on the victim’s system which enables file transfer and execution of arbitrary commands as root. Drovorub uses advanced evasion techniques since it hides artifacts from common tools used for live response.
A ransomware attack on the Dusseldorf University Hospital led to the death of a patient. As a consequence of the attack, the hospital in question was unable to take in new emergency patients, which meant that the woman in need of urgent care, had to be transferred to another hospital that was further away and thus led to her death. Ironically, the hospital was not the target of the attack but the nearby university.
The Egregor gang has released 20 MB of data allegedly related to Watch Dogs: Legion, a hacking themed video game created by Ubisoft. As of today, it is still not possible to state with certainty whether the data theft actually took place. Cybercriminals have repeatedly reported hacking Ubisoft.
On November 13, 2020, the Cigref (Computer Club of Large French Companies) sent a letter to the French Prime Minister, Jean Castex, to inform him of the concern of large French companies and public administrations about the increase, in number and intensity, of cyberattacks.
AMNESIA:33 is the name given by the cybersecurity solutions publisher Forescout to a set of 33 vulnerabilities discovered in connected objects. These vulnerabilities notably affect four open–source TCP/IP stacks (uIP, FNET, picoTCP and Nut/Net).
This content is part of our Annual Report, the Security Navigator. To download it, click here.
Sources:
https://www.zdnet.com/article/two-weeks-after-ransomware-attack-travelex-says-some-systems-are-now-back-online/
https://www.theguardian.com/business/2020/jan/13/travelex-services-begin-again-after-ransomware-cyber-attack
https://www.bleepingcomputer.com/news/security/travelex-reportedly-paid-23-million-ransom-to-restore-operations/
https://www.bleepingcomputer.com/news/security/emotet-uses-coronavirus-scare-to-infect-japanese-targets/
https://www.bleepingcomputer.com/news/security/as-coronavirus-spreads-so-does-covid-19-themed-malware/
https://www.forbes.com/sites/kateoflahertyuk/2020/03/27/beware-zoom-users-heres-how-people-can-zoom-bomb-your-chat/?sh=136fb52b618e
https://www.zdnet.com/article/supercomputers-hacked-across-europe-to-mine-cryptocurrency/
https://www.zdnet.com/article/revil-ransomware-gang-launches-auction-site-to-sell-stolen-data/
https://blog.twitter.com/en_us/topics/company/2020/an-update-on-our-security-incident.html
https://www.theverge.com/2020/9/17/21443851/death-ransomware-attack-hospital-germany-cybersecurity
https://www.securityweek.com/german-hospital-hacked-patient-taken-another-city-dies
https://kotaku.com/sources-ubisofts-watch-dogs-2-teaser-is-a-real-sci-fi-1788999298