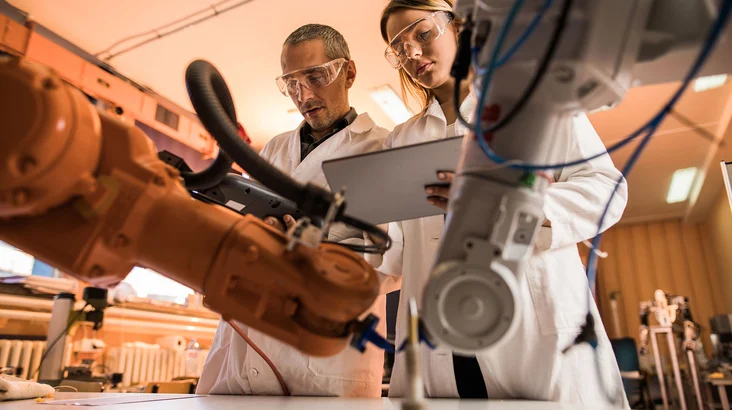
ICS Mock-up
Sensibilisierung, Prüfung und Sicherheit durch Nachbildung Ihres industriellen Systems
Trotz der Medienberichterstattung über Cyberangriffe auf industrielle Systeme ist eine Sensibilisierung nach wie vor erforderlich (Führungskräfte, Management, Produktionsteams, IT/OT-Experten ...).
Daher ist es wichtig, sie durch ein personalisiertes Modell, eine getreue Nachbildung des Betriebs- oder Produktionskontextes, für die potenziellen Auswirkungen von Hacking zu sensibilisieren.
Testlauf von Änderungen und Sicherheitsmaßnahmen in einer sicheren Umgebung
- Erhöhung des Risikobewusstseins
- Schulung über die verschiedenen Arten von Angriffen
- Verbesserung der Interaktion zwischen IT- und OT-Teams
- Planen der Sicherheitsmaßnahmen
- Testen und Validieren der ausgewählten Sicherheitslösungen
- Überprüfung der Robustheit der industriellen Umgebung
- Vorbereitung auf das Krisenmanagement
| Ihre Vorteile: | |||
Kundenspezifische Mockups:
| Diskrete Netzwerkerkennung: Scan ohne Auswirkungen auf die Produktion, um "stumme" Geräte zu entdecken | Sammlung von Konfigurationen: Wiederherstellung von Anwendungen und Betriebssystemen von Industriestationen, Hardwarekonfigurationen und Anfragen an PLCs, um eine Anwendungsvision zu erhalten. | Interviews und Besuche: Verständnis der Funktionsweise des Systems und Identifizierung der isolierten Geräte, um Schutzlösungen zu antizipieren. |
Die nächsten Schritte
Man kann nicht schützen, was man nicht sehen kann. Wenn Sie genau wissen möchten, welche Geräte sich in Ihrem OT-Netzwerk befinden und wie sie verbunden sind, oder wenn Sie Fragen zu anderen Angeboten und Dienstleistungen im Zusammenhang mit Betriebstechnik, Industrial Security oder IoT haben: zögern Sie nicht, uns zu fragen! Wir sind für Sie da, um Sie bei Ihren nächsten Schritten auf dem Weg zu einem Sicherheitsstandard zu begleiten, der Ihren Mitbewerbern voraus ist.