WAF vs NGFW
Customers regularly ask “Why do I need a Web Application Firewall (WAF) when I already have a Next Generation Firewall (NGFW)?”. The intent of this blog post is to explain the difference between both solutions with a focus on the added value that a Web Application Firewall can offer.
What is a web application?
Before explaining the actual differences, it is important to know what a Web Application exactly is. A Web application is an application program that is stored on a remote server and delivered over the Internet through a browser interface. In the early days of the web, websites consisted of static pages, which severely limited interaction with the user. In the 1990’s, this limitation was removed when web servers were modified to allow communication with server-side custom scripts. This allowed normal users to interact with the application for the first time. This interactivity allows organizations to build solutions like e-commerce, web-based e-mail, internet banking, blogs, web forums as well as custom platforms to support the business activities. All these web applications use HTTP(S) as the protocol for the connection between the web browser and the web server.
Today, web applications have become more complex, relying on languages and scripts such as HTML5, Java, JavaScript, PHP, Ruby, Python and/or ASP.NET for rich interface application, extensive frameworks and complex third-party libraries. On the one hand, these web applications are important business driving tools that are connected to the back-end databases. These databases can be a repository of company data, cardholder data or other sensitive business-related information and thus should be highly secured. On the other hand, web applications are very interesting targets for hackers as they are open and easily reachable through the internet. This presents a real challenge from a security point-of-view!
What is a Next Generation Firewall (NGFW)?
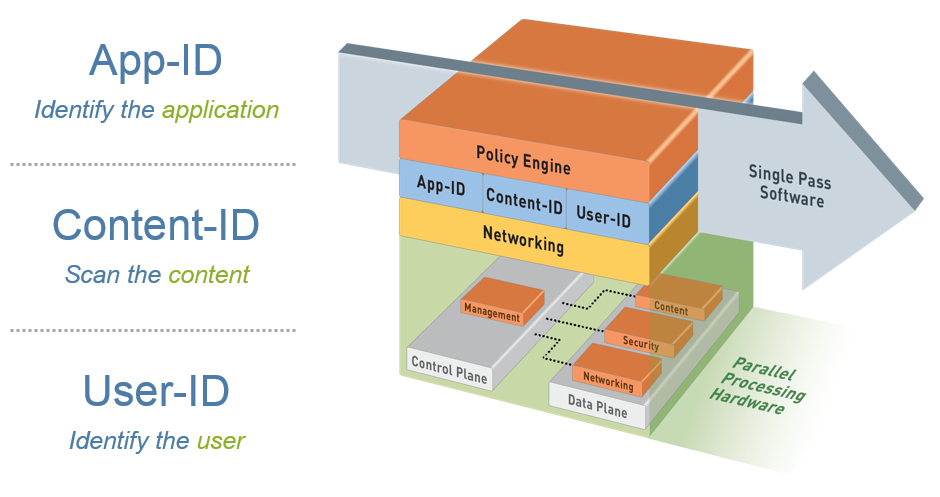
A traditional firewall is limited to functions such as packet filtering, network- and port-address translations (NAT) and VPN’s. It makes its decisions based on ports, protocols and IP addresses. Nowadays it’s no longer practical nor reliable to implement security policies in such an inflexible and non-transparent way. A new approach was needed and NGFWs provide this approach by adding more context to security policies. Context-based systems are designed to use information like location, identity, time, etc… in an intelligent way with the purpose of making more effective security decisions.
Next Generation Firewalls also distinguish themselves from traditional firewalls by adding features such as URL filtering, anti-virus/anti-malware, Intrusion Prevention Systems (IPS) and more. Instead of using several different point solutions, a NGFW greatly simplifies and improves the effectiveness of implementing security policies in an increasingly complex computing world.
What is a Web Application Firewall (WAF)?
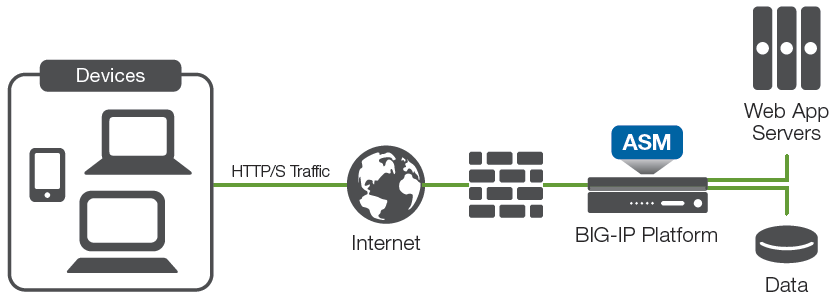
Web application firewalls protect web servers and hosted web applications against attacks in the application layer via HTTP(S) and against non-volumetric attacks in the network layer. WAFs are designed to protect a portion of your network traffic, specifically towards public internet facing web applications. WAFs can also compensate for potentially insecure coding practices by providing virtual patching for these weaknesses. A WAF is highly customizable and the setup is tailored to the specific design of a customer’s web applications. Most of the time, WAFs are installed in-line on an Application Delivery Controller (ADC).
The Open Web Application Security Project (OWASP) Top 10, the CWE/SANS Top 25 Most Dangerous Software Errors, the Web Application Security Consortium (WASC) Threat Classification v2.0 and the Cross Reference View provide a well-documented overview of the web application threat landscape. All these potential threats justify the need for dedicated Web Application Firewall technology.
What is the added value of an F5 WAF?
The custom-built character of a web application and false positives or performance hits arising from protections that rely on traffic-pattern matching can become a real issue. NGFW or Intrusion Prevention System (IPS) vendors disable most of the Web application protection signatures by default to mitigate these kinds of issues. However, NGFW and IPS vendors provide only a basic set of signatures and aren’t equipped with the more advanced features of a WAF.
The F5 Networks WAF has dedicated engines to perform traffic decoding and normalization with knowledge of web protocols and languages. Combined with more advanced SSL/TLS decryption/offloading capabilities the WAF improves the effectiveness of the extensive web attack signature database.
On top of the web attack signature database, F5 Networks offers URL, Parameter, Cookie and form protection capabilities for a deep and granular control over the user input into the web application. The implementation of the WAF security policies supported by a policy learning engine. This policy learning engine listens to the HTTP(S) requests from the clients and the answers of the web applications. In this way, a map of URL’s, parameters and web attack signatures is created to be either enforced or whitelisted.
Additionally, the F5 WAF protects your web applications through the modification of the responses sent by the web applications with techniques such as URL encryption, code injection in web pages, cookie signing and custom error pages to prevent cross-site request forgery.
As a last differentiator, the F5 WAF tracks the user sessions to detect malicious activities that can disrupt the normal business flow of a web application and it also has advanced anti-bot & anti-DDoS detection engines. Optionally the F5 Networks WAF can also provide advanced authentication services like Single Sign-on, Multi-factor authentication (MFA) and/or pre-authentication of web applications.

Conclusion
A Palo Alto Networks Next-Generation Firewall is designed to safely enable applications and protect your network from advanced cyber attacks. The NGFW is focused on securing the internal clients when accessing the application on the internet and internal applications. The focus of an F5 Web Application Firewall is the protection of internal (custom) web applications from external threats within the application layer.
SecureLink is a highly specialized security integrator, our best practice is to implement the F5 Networks WAF and Palo Alto Networks NGFW technology in a serial way within the internet access street. This best practice approach offers the best of both technologies with F5 Networks providing the SSL/TLS offloading and web application protection functionalities and Palo Alto Networks acting as an IPS and anti-virus solution for your web applications.
We can conclude by summarizing that WAFs protect web applications and NGFWs protect networks. Enterprises that rely on web-facing applications can benefit tremendously from a WAF. For these customers, it is in most cases recommended implementing both solutions.Do you have a question or would you like more information? Please do not hesitate to contact us.
