
Zero Trust: a guide to implementing a solid Zero Trust approach
In today’s decentralized reality, it has become more complex to protect corporate assets from cyber-attacks. Regulatory, reputational and geopolitical considerations pressure enterprises to safeguard their brands. The increasingly disparate, connect-from-anywhere model and the ongoing digital transformation require a new approach to security.
That approach is Zero Trust.
Download our whitepaper on Zero TrustZero Trust is an approach where implicit trust is removed from all computing infrastructure.
The three basic principles of Zero Trust
- Diligently implement “Least Privilege” throughout the organization
- Assume a breach has happened or will happen
- Authenticate and authorize every transaction
A benchmark for Zero Trust
There are five pillars that make up a Zero Trust approach:
- Identity
- Devices
- Data
- Applications and APIs
- Network/environment
Running through each pillar is automation, orchestration, integration, monitoring and governance. This allows you to manage everything without significant investment in hard-to-find human resources and cyber talent. But how do you know if what you are doing is well when it comes to your Zero Trust approach?
We have developed a framework against which enterprises can benchmark themselves and see what they need to do in order to progress on their journey. One that identifies how to obtain specific maturity levels in line with the ambition of the enterprise and its obligations towards its own customers.
Go to the framework (p.10)
A checklist to take you from theory to Zero Trust reality
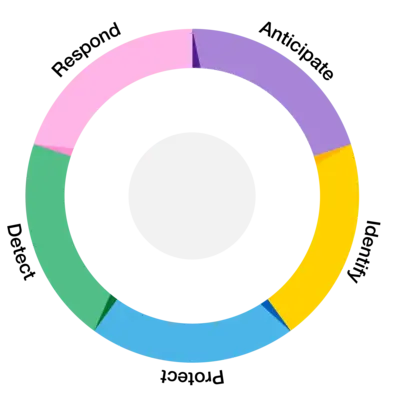
At Orange Cyberdefense, we recommend an intelligence-led approach in which you apply the NIST Zero Trust tenets across five stages of the threat life cycle. To help you get started, we have created a checklist to take you from theory to reality.
Zero Trust in action: Jan Yperman Hospital
Formed from the merger of three smaller hospitals in 1998, the Jan Yperman hospital now employs more than 1,300 employees and 130 doctors with an emphasis on technology. Its use of connected devices has increased significantly, and it was this growth that prompted the hospital to start to implement a Zero Trust approach.
Jürgen Taverniers, IT System Engineer at Jan Yperman tells you more about their Zero Trust approach in our new guide to implementing Zero Trust.
Read their story (p.15)
