Threat Intelligence: which type are you?
There are different types of Threat Intelligence. Each can be adapted to specific company needs.
As a reminder, Threat Intelligence (TI) is an advanced security monitoring system that enables us to continuously track threats and attacks so that we can better respond to them, but more importantly, anticipate them.
There are different types of Threat Intelligence. Each type is adapted to the maturity of the company’s security system and the resources (human and technological) associated with it.
Thus, there are four main ones: the strategic, tactical, operational, and technical approach.
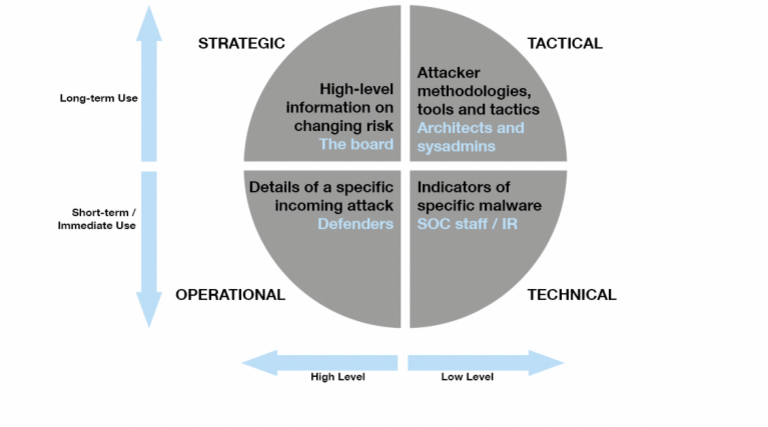
Tactical Threat Intelligence
Tactical Threat Intelligence is associated with “Tactics, Techniques, and Procedures,” also known (but more rarely) as “Tools, Techniques, Procedures.” TTPs remains the modus operandi of cyber attackers: they characterize an opponent’s actions and his way of doing things.
Tactical Threat Intelligence provides information about the behavior, habits, tools, and techniques of attackers, including malware analysis, anti-virus workarounds, and tools used to carry out Denial of Service attacks, more commonly known as DDoS (Distributed Denial of Service attacks).
Tactical Threat Intelligence thus enables us to understand the attackers’ modus operandi. Its use assists in developing proactive security devices and rapid decision making during and after intrusion detection.
Technical Threat Intelligence
Threat Intelligence involves processing a large amount of information, which most often arrives in the form of raw data and is available in vast quantities.
This data includes compromise indicators such as IPs, URLs, and hash lists. This information makes it possible to identify an attack in progress and block it more easily.
However, it is essential to know that they have a very short lifespan. Indeed, it is straightforward for an attacker to change an IP address or modify an MD5 checksum. Therefore, this Threat Intelligence is most often exploited by Security Operation Centers (SOCs) teams who supervise and protect corporate information systems.
Therefore, for reliable technical Threat Intelligence, it is better to integrate this data as quickly as possible, ideally in “real-time,” and thus in an automated way.
Operational Threat Intelligence
This type of Threat Intelligence aims to identify attacks by gathering information as close as possible to the attacker. It includes the factual list of attacks and allows to prepare for those already identified.
This Threat Intelligence is generally exploited by the security manager or incident response manager. It is less frequently used in companies and is more relevant to government organizations.
Indeed, the information collected comes mostly from forums and the dark web, which are more difficult to access. Also, many of these communities do not exchange in English, which further complicates matters.
Strategic Threat Intelligence
Strategic Threat Intelligence mainly provides access to high-level, non-technical analysis and information for decision-makers. It enables better anticipation of the defense strategies to be adopted according to the evolution of risks.
For example, it can quantify the financial impact of malicious activities or anticipate the strong trends of a period in terms of attacks. It applies to all sectors, at both the business and government levels.
In conclusion
Threat Intelligence is a real asset when appropriately used because security is now a differentiating factor in all sectors. At present, the market is mainly oriented towards technical and tactical Threat Intelligence, which improves detection capabilities.
Source:
Threat Intelligence: Collecting, Analyzing, Evaluating – MWR
