28 June 2022

Authors: Adam Ridley and Diana Selck-Paulsson
This is part three of an ongoing series on how cyber extortion (Cy-X) and ransomware threat actors utilize neutralization techniques to enable them to participate in malicious activity. In part one, we discussed our overall research approach, with part two covering the technique known as ‘denying the injury’.
As a brief refresher, neutralization techniques are ways for people who participate in a crime to drift away from accepted norms for a time without compromising societal morality (Sykes and Matza, 1957).
In this piece, we turn our focus to the technique called the ‘denial of the victim’. This is where the threat actor may seek to diminish or remove the victim’s ‘victimhood’ status. Threat actors might do this by reframing the victim as being deserving of the ransomware and extortion attack.
Sykes and Matza (1957: 668) explain that in the offender’s mind, “the injury, it may be claimed, is not really an injury; rather it is a form of rightful retaliation or punishment. By a subtle alchemy the delinquent moves himself into the position of an avenger and the victim is transformed into the wrong-doer”.
In their theoretical work, Sykes and Matza (1957: 668) also highlight how the spatial proximity between the offender and the victim affects the technique:
The existence of the victim may be denied . . . in a somewhat different sense, by the circumstances of the delinquent act itself. Insofar as the victim is physically absent, unknown or a vague abstraction . . . the [offender’s] awareness of the victim’s existence is weakened.
(Sykes and Matza, 1957: 668)
For those of us investigating crime in cyberspace, this observation is particularly important. By the very nature of the crime, people engaging in ransomware and cyber extortion attacks are rarely physically close to their victims. As such, the spatial (and mental) distance between threat actor and victim may contribute to a threat actor’s ability to diminish or deny the existence of a victim (see also Smith and Stamataakis, 2020).
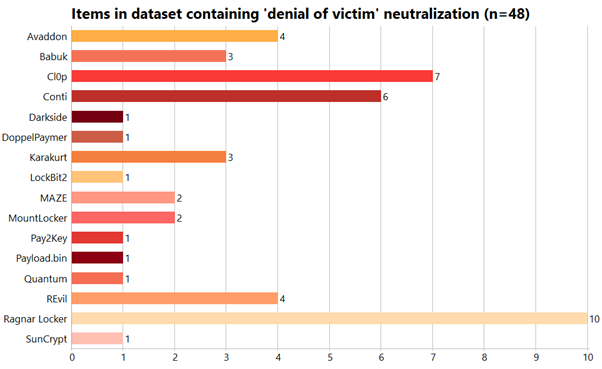
As displayed in Figure 1, we observed this technique being employed in 48 unique documents from 16 different threat actor groups. Across these 48 documents, we observed this technique used on 86 unique occasions.
The main theme relating to the denial of the victim that emerged from our data was when threat actors described themselves as ‘vigilantes’. The strongest form of this was when they accused victims of being corrupt or engaging in unethical business practices. Cyberattacks and extortion were then construed to be a justified punishment.
Another variation of the vigilante theme was when threat actors portrayed their victims as being negligent or reckless with information security. Threat actors then argued that the vigilante behavior (i.e. cyberattacks) would force these companies to reform their practices.
The second theme we found was a form of victim-blaming. Threat actors suggested that victims were not really victims because of their choices in response to the cyberattack. This was done by arguing that it was the victim’s own fault when data was leaked. For instance, if a victim chose not to negotiate the ransom, it was this decision that then led to further consequences.
On some other occasions, we also observed one further theme where threat actors’ discourse implied that a victim could not have victimhood status if they were a ‘customer’ engaging in a legitimate business transaction. As we foreshadowed in the previous piece, there is a close overlap between denying the injury and denying the victim (see Figure 2; see also Brewer et al, 2020: 554).
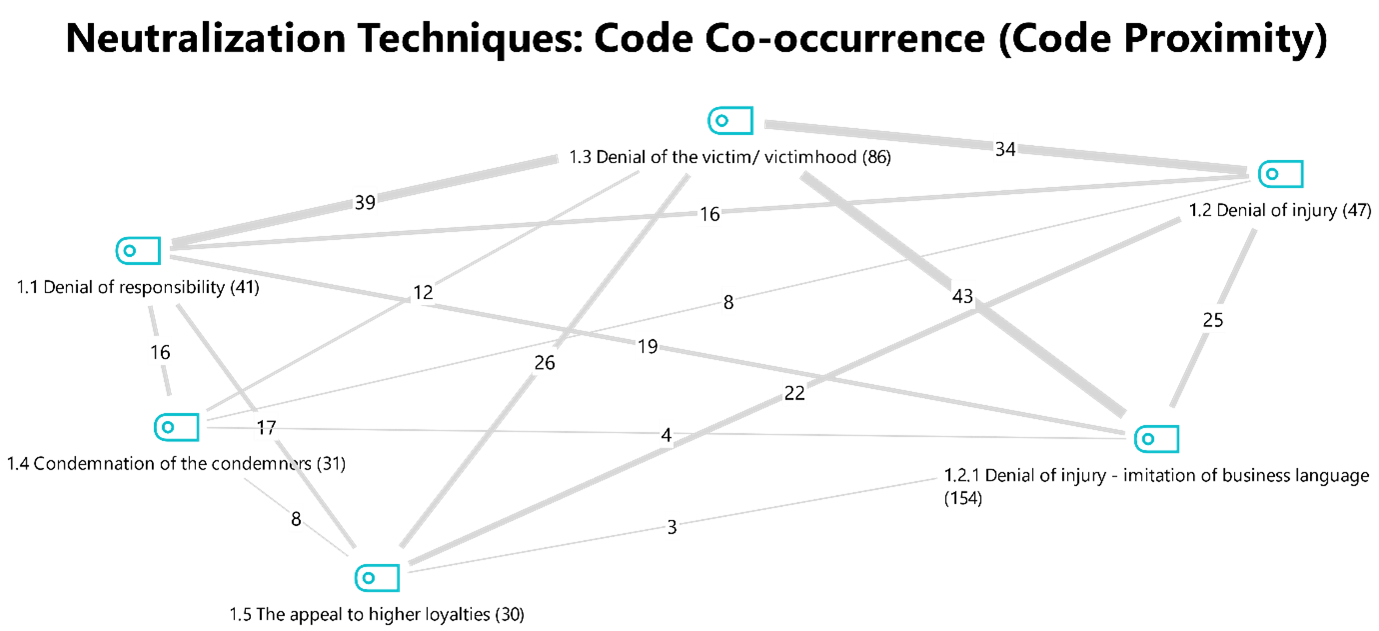
In light of the overlap with the denial of injury and the imitation of business language, this piece will not seek to cover the same ground twice.
In addition, please note once again that the quotes included below from threat actors have not been edited for grammar or syntax.
One of the most straightforward approaches that a threat actor can employ to deny the victim is to redefine the victim as an entity that deserves the attack. In doing so, the threat actor positions themselves as a vigilante, exacting righteous justice.
In our dataset, we found two distinct strands of this behavior. The first was where victims were described as being corrupt or as engaging in unethical business practices that would subsequently be revealed in data leaks. The cyber extortion attacks were then construed to be a justified punishment on a deserving ‘wrong-doer’. The threat actors that we observed employing this neutralization most frequently were Cl0p and Avaddon.
For example, Cl0p used their leak site to denounce one of their victims who they accused of corporate espionage:
They steal USA company technology and make it like they are own and make it cheaper and cause USA company to go out of business... [REDACTED COURT] making the final verdict on two patent infringement cases and one trade secret infringement case between [REDACTED THIRD-PARTY COMPANY NAME] and [REDACTED VICTIM COMPANY NAME]... but nowadays they steal even more because they know they have money and can pay little to make a lot more.
This example of corrupt company who manipulate market and steal knowledge... Cl0p fix all this and we make bad corporation pay for their crime even when corrupt government does nothing.(Cl0p, Leak Page 2)
By labelling the victim as company that engages in corporate espionage, Cl0p implicitly positioned themselves as being a justified vigilante. This is because Cl0p framed the victim as being corrupt and manipulative because they had been stealing intellectual property from other organizations.
However, Cl0p went even further by explicitly assuming the role of vigilante that will punish the “bad corporation” for their crimes because “the corrupt government does nothing”.
Similarly, Avaddon also explicitly assumed this role in the quote below:
This time we will be in the role of Robin Hoods. [emphasis in original] Today we will give light to the world on a company that does very bad things.
Pay attention to the document, on it we can see how a certain [REDACTED NAME] a board member at [REDACTED THIRD-PARTY COMPANY NAME] negotiates with the management of [REDACTED VICTIM COMPANY NAME] about how to illegally receive money from the accounts of the deceased family during the accident.(Avaddon, Leak Page 5)
The excerpt began with Avaddon drawing a direct parallel between themselves and the mythos of Robin Hood. This construction is actually specifically highlighted by Sykes and Matza:
. . . but Robin Hood, and his latter day derivatives such as the tough detective seeking justice outside the law, still capture the popular imagination, and the delinquent may view his acts as part of a similar role.
(Sykes and Matza, 1957: 668)
In this way, Avaddon can be observed directly following the pattern of behavior described in the original theoretical text. They described allegedly illegal conduct between a third party and the victim, using this as leverage for the extortion threat. As such, Avaddon appeared to be portraying themselves as a vigilante, shining light on corrupt conduct (albeit with an ulterior financial motive).
On another leak page, Cl0p followed a similar pattern by describing themselves as a noble vigilante figure that exposes lies and corruption:
Many year ago like 2019 they have ransomware attack. now in 2021 they have another. lesson learn? no. clients who use [REDACTED COMPANY NAME] are no smarter maybe very stupid. smarter IT person beg for forgiveness and offer equivalent of burger and milkshake. They also own [REDACTED COMPANY NAME] data center and website claim 650,000 customer but they say they make no money they in charity business we guess. Cl0p is here to expose all lies and companies who all do is steal under the guise of normal business.
(Cl0p, Leak Page 6)
Cl0p repeated this pattern time and time again. In the quote below, they called out ‘creative accounting’, which implied that the victim was evading tax or engaged in unethical financial dealings.
o sins of some companies. we lock this company real tightly. we take some juicy secrets that we post very soon. IT guys try to hide to management because they have backup. But what is interesting is some creative accounting of this company.
(Cl0p, Leak Page 3)
Moreover, the use of the term ‘sins’ is particularly noteworthy here. The negative connotation of this word is designed to strip the victim of their victimhood status, as sins need to be ‘cleansed’, ‘atoned for’, or even require ‘divine retribution’. By doing this, Cl0p was able to position the victim as being a deserving target for the cyber extortion attack. Simultaneously, this enabled Cl0p to claim legitimacy for their vigilante actions by framing their attack as being a positive moral act, which in turn neutralizes the moral dissonance of engaging in criminal activity.
The second way that we observed threat actors positioning themselves as vigilantes was when they argued that their victims were negligent or reckless with information security. Scholars have previously linked this argument to the denial of the victim technique, as Chua and Holt (2016: 539) explain:
The end users’ inability to keep their systems safe from compromises or understand how they operate are used as a justification by some to engage in system compromises and malicious hacks.
(Chua and Holt, 2016: 539)
The subsequent vigilante behavior (i.e. cyber extortion attacks) is then intended to force companies to reform their practices. Maze displayed this type of neutralization very frequently, though we will also explore examples from Ragnar_Locker, Karakurt and SunCrypt.
In their public announcements, Maze frequently argued that victim organizations did not understand the importance of protecting sensitive data. Maze used this lack of awareness to justify the cyber extortion attack in order to improve victims’ cybersecurity practices.
But sometimes companies can’t understand the risk of information leak, especially the private information. We are specializing in client’s private information, financial information, databases, credit card data, NDA documents and all the company’s researches . . . We just can’t understand what cybersecurity [REDACTED COMPANY NAME] are talking about as they have an Australia size security hole in their security perimeter.
(Maze, Press Release June 2020)
In another press release, Maze expressed disbelief at the technical incompetence of a victim:
In those 2 days company’s security didn’t even check the enormous activity inside the company’s network. But despite of that, all the breaches inside the security perimeter are still open. That’s not because of COVID. It’s just the the laziness and absence of any will to do something.
(Maze, Press Release April 2020)
In another example, Maze told a story about some IT specialists and network administrators that allegedly sought to hide the extent of a data leak. They did this by attempting to sell to Maze compromising information about their executives or data from other companies.
Another word for the IT specialist and network administrators who are tring to hide the information of the data leak from the company’s executives. They are making everything just the worst. We were really shoked by the fact that some network administrators were trying to hide the leak by offering us the access to the data of other companys, access to private laptops of the company’s president or even the naked photos of their boss’es secreteary. Funny but it’s true.
(Maze, Press Release March 2020)
In their final press release announcing the closure of their operations, Maze explicitly drew the connection between their supposed vigilante behavior and the negligence of organizations:
WHY? Our world is sinking in the recklessness and indifference, in laziness and stupidity. If you are taking the responsibility for other people money and personal data then try to keep it secure. Until you do that there will be more projects like Maze to remind you about secure data storage. (Emphasis in original.)
(Maze, Press Release November 2020)
In this manifesto, Maze used terms like 'recklessness', 'indifference', 'laziness' and 'stupidity' to describe and characterize their victims. In doing so, Maze was then able to position themselves (and other threat actors) as being 'moral avengers' who expose poor information security practices to ultimately make the internet safer. This is reinforced by choosing to refer to themselves as a ‘project’, since projects intrinsically have objectives.
Ragnar_Locker made similar claims on five separate occasions in our dataset. For example:
Another example of the company's indifference to the responsibility for the protection and safety of information. We did notified company about the security breach and honestly gave them chance to fix the "bugs" and avoid data leakage, however they are not interested about that.
(Ragnar_Locker, Leak Page 2)
Unfortunately even such worldwide known company as [REDACTED COMPANY NAME] doesn't values much privacy and security. They was notified about vulnerability and data leak numerous time.
(Ragnar_Locker, Leak Page 3)
In the quote below, Karakurt also accused their victims of negligence:
Dear visitors, customers and journalists
Our third volume of companies working in different industries and who failed to protect their data - at your service.
(Karakurt, Leak Page 3)
In this quote, Karakurt reframed their victims as being at fault for “[failing] to protect their data”. The victims were no longer victims, but instead were culpable parties responsible for their own misfortune since information security is something that is so critical and important.
SunCrypt went further though in one post by condemning the incompetence of a victim from the IT and cybersecurity industry:
The company that claims to offer IT solutions and network and security audit services actually offers you the loss of your data and GDPR non compliance responsibility. As long as they are incapable of protecting their own network. . . . You have TRUSTED them and they FAILED you.
(SunCrypt, Announcement 1)
SunCrypt’s scathing assessment portrayed their victim as not caring about privacy, information security or GDPR compliance, labelling the victim’s attitude as negligent and reckless. By doing this, SunCrypt appears to be shifting blame and responsibility onto the victim.
Similarly, REvil adopted nearly identical language in their critique of a different victim from the IT industry:
Your customers have entrusted you with the most valuable thing - their backups and data for storage, but you have not coped with your task. . . . We drew conclusions that you are not worthy to provide IT and Print Solutions (everything for which you are responsible). Your customers should be ashamed of you. You are disrupting both your reputation and the reputation of people who have trusted you with their safety.
(REvil, Leak Page 3)
REvil’s choice of language here appeared to indicate that because the victim was an IT service provider, they were doubly deserving of the pain inflicted by the ransomware and cyber extortion attack.
However, we have also found evidence in the dataset that appears to run contrary to the assertion that REvil uses this particular neutralization technique of denying the victim:
INTERVIEWER: Do you feel like Robin Hood?
REvil: Honestly? No. I am against romanticizing my work. Money is being stolen or extorted with my hands. But I’m not ashamed of what I do. I sincerely try to find at least something bad in this and cannot. Probably, my concepts of what is good and what is bad are somehow shifted. But in this case, they are shifted for many in this profession.
(REvil, Interview 3)
In this short extract, we can see an explicit rejection of the ‘Robin Hood’ or vigilante complex. Now, it is possible that the person from REvil being interviewed here was different from the person who wrote the text in Leak Page 3. As such, it is plausible to suggest that at an individual level, both accounts can be accurate and valid simultaneously.
Yet, the interview extract does raise some important questions. Can we as observers trust the validity of any evidence of neutralization that we find? Or does this vigilante complex serve some other purpose, perhaps as a façade?
The short answer is that we must analyze the dataset at face value and not infer more than what can be supported directly from the text itself. Yet this must be also be balanced with a critical interpretation of what is going on ‘behind’ and ‘within’ the text – an approach social scientists call ‘hermeneutics’. The context and subtext of the quote must always be taken into account, insofar as this is possible.
With this in mind, we can see that the voice of who is ‘speaking’ is one major difference between the REvil leak page and the REvil interview. On the leak page, the voice is that of REvil the organization, speaking to a much wider public audience. For the interview, the voice is the individual who works for REvil but speaking for themselves as an individual to an interviewer.
If we consider the approach of dramaturgical analysis that we mentioned in our previous post (Goffman, 1959), people behave in different ways when they assume different roles. The apparent contradictions can then make more sense once REvil’s seemingly divergent behaviors are conceptualized along these lines.
Therefore, threat actors may feel a need to engage in public-facing neutralization techniques for pragmatic or strategic purposes. For example, it might run counter to their organizational ‘self-image’ or business model to explicitly state that they exist solely to extort money from victims. Or perhaps there is a moral ‘disconnect’ between the upper hierarchy of REvil who control the public image, and those who work at lower ranks within the organization.
It is particularly important though to see the interview participant from REvil demonstrate a remarkable self-awareness of their own criminality and the way that this has affected their own personal understanding of morality. Perhaps then, the lure of money and financial gain can be seen as more dominant than a moral code that is no longer being upheld.
The second theme to emerge from the dataset was that threat actors used victim-blaming language in response to the victim’s behavior after the ransomware infection occurred. In particular, threat actors often argued that it was the victim’s own fault if a data leak had occurred because the victim had chosen to not negotiate the ransom payment.
For example, Karakurt shifted responsibility for a data leak onto victims in an attempt to absolve themselves:
We always try to do our best to keep company`s privacy safe from the beginning, like the data breach never happened. These companies had a choice to keep everything under the secret or being publicly disclosed. Our victims above have chosen to be punished.
(Karakurt, Leak Page 2)
The key phrase here is “Our victims above have chosen to be punished”. The function was to suggest that the agency for the data leak lay solely with the victims and their decision to pay the ransom (or not). If the victims choose not to pay, this gives the threat actor the ability to claim that their hands were tied and that there was no other option available but to publicly leak the data.
On Leak Pages 2 and 7, Ragnar_Locker actually formalized this rhetorical device by claiming that “according to our rules”, the data had to be leaked since the victim had refused to pay a ransom. Therefore, it was ‘the rules’ that determined the required course of action, even though the threat actor wrote those rules themselves. The rules, as an abstract construct, then enable the threat actor to put some distance between themselves and the responsibility for their actions.
In another negotiation chat, DarkSide also sought to weaponize the threat of a data leak to intimidate the victim into paying the ransom:
Support: Our other clients can pay in this time, if you want - you can not pay, we need publications for the blog.
Support: Your data leak will be a good reason for other companies to pay us.
(DarkSide, Negotiation Chat 1)
Conti took a similar approach in a negotiation, lashing out at the victim after the victim was not providing ‘reasonable’ offers for the ransom payment:
No, we are not satisfied, these are ridiculous numbers. In 3 days we will start to publish your data on our website and send it to interested parties, also this chat will be deleted, in the future you will not be able to get a transcript. . . . We always make concessions. It seemed to us that you decided to play with us by naming such amounts. Have a good day and good luck.
(Conti, Negotiation Chat 24)
As we can see, this use of language attempt to divert responsibility and blame away from the threat actor and onto the victim. The goal appears to be to diminish the victim’s claim to legitimate victimhood status. Likewise, it is also a way for threat actors to assert their power over the victim.
By establishing ‘rules’ that must be followed by victims, threat actors implicitly highlight that they are the ones in control of the situation at all times. This leaves the victim little choice: either go along with what the threat actor wants, or face the consequences (e.g. a public data leak).
This is not quite as overt or direct as the justifications we saw earlier, where the threat actor assumed the role of vigilante to punish corrupt, reckless or negligent behavior from victims. However, the intended effect is the same: neutralizing the existence of an innocent victim so that the threat actor can suspend their adherence to the “moral restraints of society” (Brewer et al, 2020: 549).
In line with Sykes and Matza’s theory of neutralization, the discussion above highlights how people who engage in cyber extortion can seek to deny the existence of a victim or diminish a victim’s claim to victimhood.
We observed this behavior through two main ways. The first was where the threat actors would seek to portray their victims as being deserving of punishment due to a victim’s alleged corruption or negligence. Because of this, the threat actor could then position themselves as a vigilante, characterizing their extortion attacks as exacting righteous justice.
The second approach was perhaps more blunt, with threat actors sometimes attributing blame for data leaks directly on the victim’s choice to not pay a ransom. In doing so, some threat actors appeared to be absolving themselves of responsibility for the consequences of the data leak.
We also found some commonality between these two themes. On occasions, threat actors sought to characterize victims that did not negotiate or pay a ransom as being greedy, reckless or negligent. If we turn to Goffman (1959) one more time, it appears that victims are expected to stay within the role set out for them by the threat actor. Although the amount of the ransom payment might be negotiable, the ‘rules of engagement’ certainly are not.
Moreover, there is some further scope to consider how threat actors frame the temporality of victimhood. That is to say, at what point in time does a victim become a victim? Some of the so-called victim-blaming language implied that ‘victimhood’ began only with the public leak of data, but not at the point of encryption or data theft.
By temporally reframing an attack, threat actors seem to suggest that the actions that occurred prior to the public leak could be viewed as being a non-attack. Once again, we see some overlap with the denial of injury technique from our previous paper. In doing so, such a denial seeks to redefine what constitutes victimhood (and what does not).
In the next piece, we will discuss the neutralization technique known as ‘condemning the condemners’, where we have observed some similarities with the victim-blaming tactic. By appearing to divert attention and responsibility to third parties, there is evidence to suggest that threat actors sometimes try to shift the spotlight away from their own culpability for their actions.
Brewer R, S Fox and C Miller (2020) ‘Applying the techniques of neutralization to the study of cybercrime’, in T Holt and A Bossler (eds), The Palgrave Handbook of International Cybercrime and Cyberdeviance. Palgrave Macmillan, Cham, pp 547-566.
Chua, Y T and T J Holt, ‘A Cross-National Examination of the Techniques of Neutralization to Account for Hacking Behavior’, Victims & Offenders, vol 11, no 4, pp 534-555.
Goffman, E (1959), The Presentation of Self in Everyday Life, Doubleday, Garden City, NY.
Smith, T and N Stamataakis (2020), ‘Defining cybercrime in terms of routine activity and spatial distribution: issues and concerns’, International Journal of Cyber Criminology, vol 14, no 2, pp 433-459.
Sykes, G M and D Matza (1957), ‘Techniques of neutralization: A theory of delinquency’, American Sociological Review, vol 22, no 6, pp 664-670.