
Modern SOC Series - From Fragmented to Focused: evolving the SOC for better outcomes (2/4)
8 July 2025

Modern SOC Series - From Fragmented to Focused: evolving the SOC for better outcomes (2/4)
8 July 2025
Artificial intelligence: from innocence to governance - 8 minutes to stay in control

Calculated, profit-seeking cybercrime activity peaks at 35-44 years old
4 March 2026

AI Powered SOC Transformation: The Next Evolution of Defence
AI Powered SOC Transformation: The Next Evolution of Defence
Event detailsIn-Person
28th of Apr

Security Navigator for Business Leaders
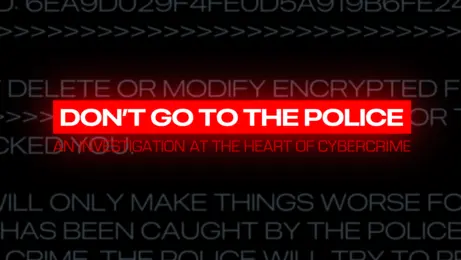
Premiere: Don't go to the Police
Premiere: Don't go to the Police
Event detailsLive event
18th of Mar

8-minutes-to-stay-in-control: Quantum and security

Discovering Security Navigator 2026 From Headlines to Hard Truths: Cyber Extortion, Threat Actors, and What You Can Do
Discovering Security Navigator 2026 From Headlines to Hard Truths: Cyber Extortion, Threat Actors, and What You Can Do
Event detailsOnline
11th of Feb

Stolt-Nielsen implements fully integrated Orange SASE solution to optimise global connectivity and security for a hybrid workforce
1 June 2025

6 of 6 - Forging forward with GenAI
6 January 2026