Videos
Webcast:
The journey to secure your IT/OT convergence
From a governance perspective more and more C-levels require IT staff to secure OT systems. Alignment between these two worlds, using entirely different sets of technologies and tools without any appropriate communication, remains a main challenge to ensure a successful cybersecurity transformation.
Hear different perspectives on how to drive IT-OT alignment in your cybersecurity projects by using concrete tools and methodologies for both and by implementing best practices and establishing the lines of communication between the two worlds.
Watch the recording on demandWebcast:
SolarWinds incident: When faced with the inevitable, embrace a new way of thinking
In this session, Charl van der Walt, Head of Security Research and Nicolas Arpagian, Director of Strategy & Public Affairs, will explore the real causes and implications of this incident and why businesses, who don’t know if they have been impacted, should not ignore the signals and instead embrace a new way of thinking and approaching security.
Watch the recording on demandWebcast:
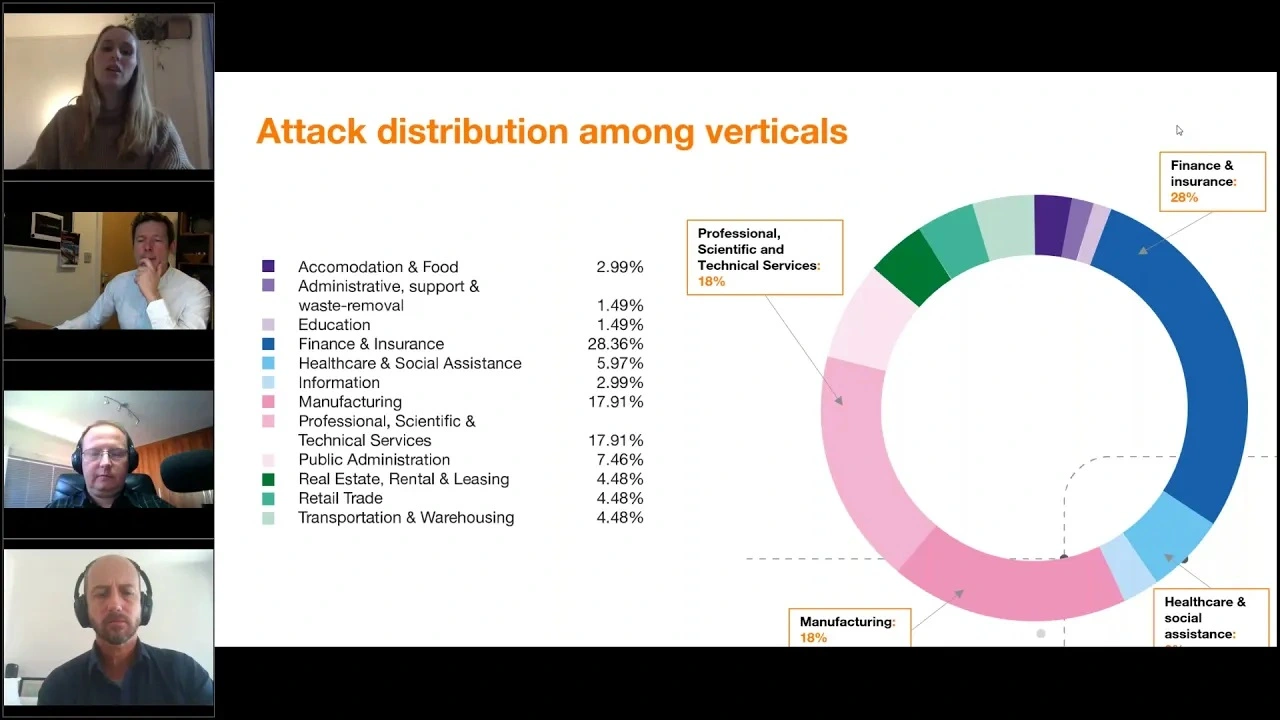
Security Navigator 2021: Research-driven insights to build a safer digital society
In this session Charl van der Walt, Head of our Security Research Centre, and his colleagues, Wicus Ross and Diana Selck-Paulsson, will take you through the most intricate and surprising research findings and the threat model which they developed thanks to 100% first-hand intelligence obtained from the 17 global SOCs and CyberSOCs of Orange Cyberdefense globally.
View the recording on demandWebcast:
Endpoint security & incident response: What did we think was going to change with COVID-19?
What specifically are the new challenges and what should professionals be thinking about as work-from-home becomes the new ‘normal’? In truth many of the dire predictions made at the start of the crisis have proven to be a little exaggerated.
What does seem clear is that a large scale and permanent remote work paradigm does present a new set of challenges for certain key security practices, specifically Remote Access, Endpoint Detection & Response, and Incident Response.
View the recording on demandWebcast:
How the shift to home-working impacted the challenge of vulnerability management
More than ever ‘remote’ systems are taking-over the frontline in the cybersecurity battle, and at the same time they are further beyond our control than we’ve ever been used to.
One area that all of this directly impacts is Vulnerability Management. Today it’s essential for businesses to shorten the patch cycles on key assets, including remote endpoints, cloud and VPN systems. VM programs have had to pivot from managing systems local to the enterprise network to encompass systems largely connected via the VPN or located somewhere in the cloud.
View the recording on demandWebcast:
Cybersecurity in a lockdown – Does the new context favour the attacker or the defender?
Many fundamental security realities are not really changed by the pandemic. However, some critical challenges, particularly those concerning our own ability to monitor and respond to threats and vulnerabilities, have become considerably more difficult.
On the other hand, we should note that the attacker is also human and that attacker behaviour may also shift due to the impact of the virus, perhaps even reducing the level of threat at this time. How do we assess how our current level of threat is impacted by the COVID-19 pandemic.
View the recording on demandWebcast:
COVID-19 A biological hazard goes digital
As the COVID-19 coronavirus pandemic continues to spread worldwide, cyber threat actors are trying to capitalize on the global health crisis by creating malware or launching attacks with a COVID-19 theme.
However, this kind of exploitative behavior by the cybercrime ecosystem is only one part of a bigger cybersecurity picture. Orange Cyberdefense is releasing this paper in order to draw attention to a diverse set of considerations that should be made now.
View the recording on demand